Securely Exposing Homelab Projects
No, this is not another Cloudflare Tunnel tutorial
Sometimes you have to expose your homelab projects to the world wide web. But how do you do that safely? Punching holes in your network can be scary and can lead to security vulnerabilities.
Although there are many approaches to securely exposing your web app or project, I am going to talk about how I do it in my homelab.
Granted, my way may not be “the best” way. Every homelabber now seems to only use cloudflare tunnels (which are fine). But I am taking a different approach.
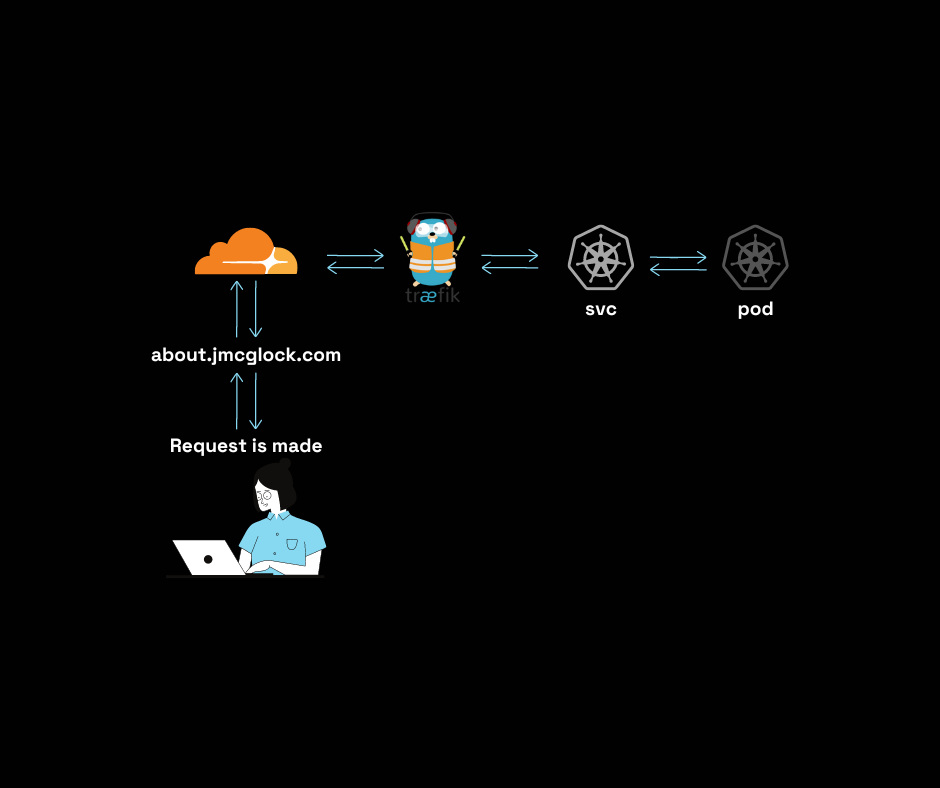
Here is my setup:
A user makes a request
The request goes to Cloudflare DNS
The request is directed to my public IP
The request is ingested by Traefik and routed to the correct Kubernetes service
The Kubernetes service routes the request to the correct Kubernetes pod
The request makes its way out in the reverse order
So does that mean that my public IP is out there chilling?
Not exactly.
I have firewall rules on my UDM Pro that will only allow traffic if it is coming directly from cloudflare. No one can directly access my public IP. You can find a list of cloudflare IPs here.
The next hop in this scenario is the Traefik load balancer service IP.
But what do the firewall rules look like? Simple.
I have 15 rules. One for each CF IP in the list.
I am opening port 80 on IP 10.0.0.210 (traefik lb). I am only allowing TCP as well.
And that is how I do it. It’s simple because I only have to port forward one IP and it’s not even a server IP.
Let me know what you think.
Cheers,
Joe